10+ Important IT Policies and Procedures Examples to Download
Information technology is one of the most important and largest departments of a company. They have the most important role in the company as they manage all technologies and systems of the company as well as all electronic information and critical data. It is important that a company should implement a policy and procedures in regards to this matter as this will set out rules and regulations to maintain the security and to control lapses concerning information technology.
IT and Software Company Work from Home Policy Template
IT Software Asset Management Policy Template
BYOD (Bring your own device) Policy Template
In this post, we will cover 10 of the most important IT policies and procedures that a company should have for their policy proposal, once they understand its importance as a foundation for data security.
Free IT Charging Policy Template
Free Software Usage Policy Template
Acceptable Use Policy

The Acceptable Use Policy or AUP is a policy that ensures all employees knows the acceptable use of technology. This policy covers defining company’s resources that has something to do with technology, such as the computers, servers, computer networks, communication and mail servers, and other resources that need technology to run. The Acceptable Use Policy should cover these important areas:
- Employees access to computers
- Use of computer resources
- Computer security
- Password protection
- Email and internet usage
- Data communication
- Accessing of inappropriate or unlawful material
- Changing or altering confidential information
- Sharing confidential information or intellectual property
- Using other’s access and files
- Installing of any software that may or may not affect the company
- Monitoring of computer resources and computer logs
- Secure remote login
- Storing and back up of files
Security Awareness

Security Awareness policy aims to inform all users the result of their actions regarding on security and privacy. This policy ensures that all computer security risk is being handled and control. Some of the actions that this policy covers to reduce related risks and cut down the cost of security incidents are:
- Implementing security policies
- Blocking unauthorized access to networks and computers.
- Improving security awareness
- Early detection and mitigation of security risks
Information Security
Information Security policies are sets of rules and regulations that lay out the framework for the company’s data risk management such as the program, people, process, and the technology. Specifically, this policy aims to define the aspect that makes the structure of the program.
These aspects include the management, personnel, and the technology. But, the most important part of this policy is the point of contact that is responsible for information security. This could be the IT manager, IT specialist, technical consultant, or the data analyst. However, the company may have the right to assign someone even if he/she is not part of the IT management.
This policy covers the following:
- System access control
- Information access
- User IDs and passwords
- Password policy
Backup and Storage
Another important IT policy and procedure that a company should enforce is the backup and storage policy. Electronic backup is important in every business to enable a recovery of data and application loss in the case of unwanted and events such as natural disasters that can damage the system, system failures, data corruption, faulty data entry, espionage or system operations errors.
This policy set rules and regulations for the backup and secure storage of all critical data and electronic information of your company.
Change Management

The purpose of this policy is to ensure that all changes made are managed, verified, approved, and tracked. Since the system and software are being updated and modified as per requirements of the company and for a number of different reasons, it is important that all of these are managed and tracked by the company to ensure that all things are running smoothly and without a problem.
Without the change policy, a company may not able to track the cause of unexpected risks such as data loss, data corruption, or data leaks that are caused by a change of software or from the updated system. This policy also assures that all users completely understands all the change and its possible impacts to all data and systems.
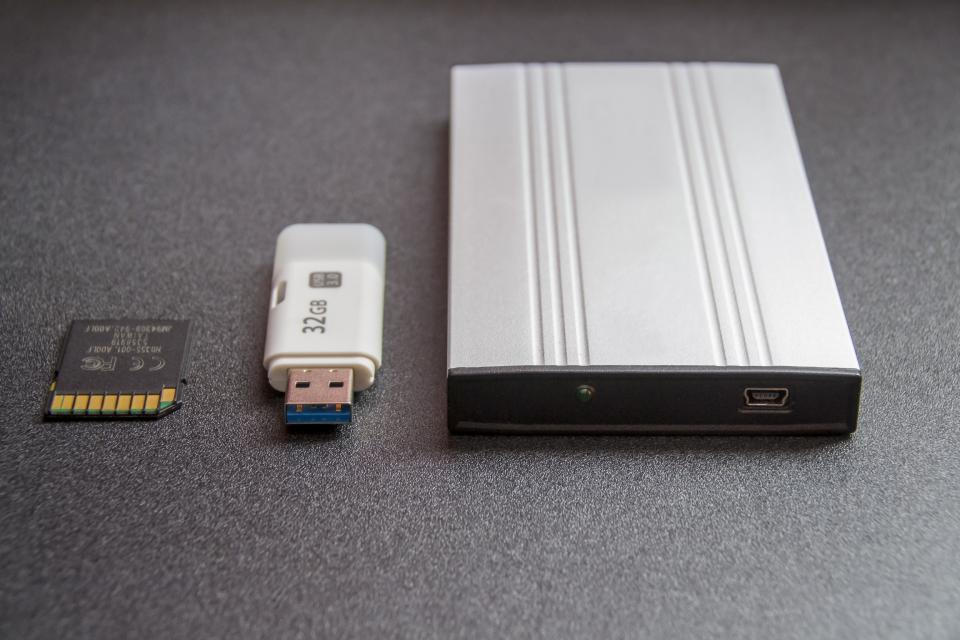
BYOD

BYOD or “bring your own device” policy is a policy that allows all employees to bring their own devices such as laptops, tablets, and smart phones to the workplace and to use those devices to access privileged company information and applications.
Requirementssmartphonesicy include the following.
- All device must use the approved operating system.
- All device must save passwords in an encrypted password store.
- All devices must be configured with a secure password that complies with company’s password policy.
- Outside devices are not allowed to connect directly to the internal company network.
Remote Access

A company must also set forth a policy that addresses the need to develop standards to protect the company’s network in allowing remote access. This policy is critical as the space constraints, remote offices, teleworkers, and outsourced vendor activities are increasingly growing and the Remote Access policy should cover these concerns.
The Remote Access policy aims to define those standards for connecting your company network to any internal and external host. These standards are made to decrease the vulnerability of your company from any threats and risks that are caused by unauthorized use of your company resources, an important next step after running a risk analysis.
Vendor Access
Vendor plays an important role in support of your company’s hardware and software management and customer’s operation. The Vendor Access policy defines the basic requirements of your company’s information system vendor management and aims to set rules and regulations for vendor access to your company’s information system and support services such as fire suppression, PDU, A/C, UPS, etc. This policy also establishes rules for the vendor responsibilities and the protection of your company information.
Incident Response

The Incident Response policy ensures that all physical system of the company is safe from any internal or external attacks. it covers everything from an infected desktop, laptop, smartphone or a DDoS (Denial Of Service) attack to the violation of computer security policies, acceptable use policies, or standard security practices. This policy should include the following actions:
- Creating an incident response policy and plan.
- Setting guidelines and rules for communicating outside parties that involve any incidents.
- Devise a method for handling and reporting any incidents.
- Choosing an appropriate team structure and staffing model.
- Setting secure relationship and lines of lines of communication between the incident response team and other
- internal and external groups.
- Determine the appropriate service or solution that the incident response team should provide.
- Training the incident response team of what are the appropriate actions to do.
DR/BCP (Disaster Recovery, Business Continuity Plan)

The DR/BCP helps the company to manage and control the security risk in real-time. This means that the company is ready and have all the right possible solution for any risk that the company may face. This includes everything from computer threats such as denial-of-service attacks, data corruption, software hack, malware attack, etc. to physical threats such as floods, fires, hurricanes or any other potential disruption of service.
This policy aims to keep the business up and running no matter what threats and risk the company may face. Moreover, the DR/BCP must always involve the business units every time the company may conduct planning and testing.