10+ Security Risk Assessment Examples to Download
Reality or in a cyber reality, the main thing to always remember is that the stronger the security, the less issues and risks people are going to be dealing with. However, if the security is weak, there are going to be issues like hacked accounts, viruses and even stolen information to be used for something else. It goes without saying, having strong security control should always be considered as something important. Some people may think that the data they have could not be taken away or deleted if the security on their computer is good, but even looks can be deceiving. There is a way for you to know if your security is at risk or is far from it, and to do this you must do a security risk assessment. Check out the article below for more information.
10+ Security Risk Assessment Examples
1. Security Risk Assessment for Public Transit
2. Standard Security Risk Assessment
3. Information Security Risk Assessment
4. General Security Risk Assessment
5. Organizations Security Risk Assessment
6. Risk Assessment for Personal Security
7. Security Risk Assessment Summary
8. Security Risk Assessment in PDF
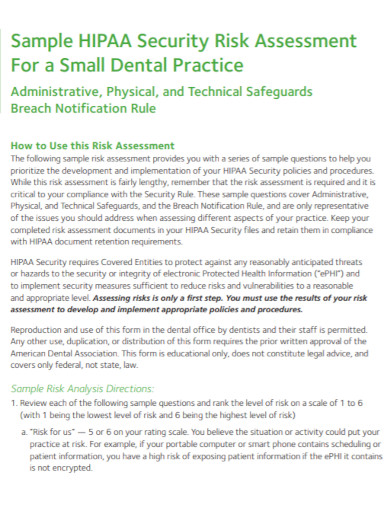
9. Security Risk Assessment for a Dental
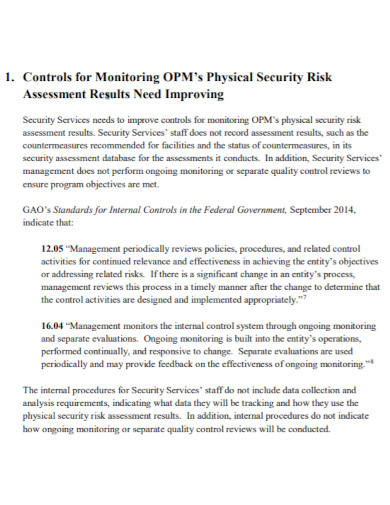
10. Physical Security Risk Assessment
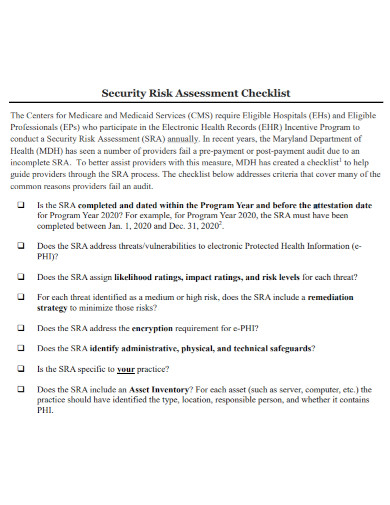
11. Security Risk Assessment Checklist
What Is a Security Risk Assessment?
A security risk assessment is a kind of assessment that investigates, identifies, assesses and finds a solution to the problem. For this case, it would be a security problem. A security risk assessment helps lessen the risks that are involved. This could be in the form of an issue on the computer or anything that can be breached for its security. A security risk assessment helps search for a solution to what problem or issue it may be facing at the moment. In addition to that, a security risk assessment gives the assessor a view of where the weaker parts of the system may be and to find a way to make it less so. This also gives the assessor a chance to see how to make security issues better in case of any issues that may cause it to be a problem.
How to Write a Security Risk Assessment?
Moving on, we already know what a security risk assessment is. As well as we know what a security risk assessment does. What we have not know is how do you write or how do you do a security risk assessment. Just like any other type of risk assessment, a security risk assessment has steps or ways to let you do the assessment. However, what is being written here are suggestions when you want to begin writing one. How you are going to apply these suggestions to your risk assessment is up to you.
1. Gather Data
To begin doing a risk assessment, one must first gather some data. Gather enough data and information that supports the assessment you are about to do. In addition to that, gathering enough data or information can also be useful as the more data you have, the more solutions you may be able to do. Without the gathered data, your assessment is useless. So in a way, your data is the brain of your assessment. The most important puzzle piece to your risk assessment.
2. Identify the Issues
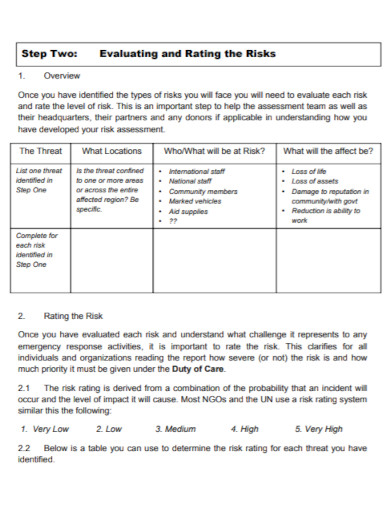
After gathering all the necessary data, the next thing that can be done is to identify the issues. Identify what is causing the problems and understand the level of severity the following problems or issues face. This is also the best way to know which issue is manageable and which issue may need a lot of attention and could be very severe if left alone.
3. Analyze the Problems
Using the assessment, begin to analyze the problem. This also helps the assessor find any loopholes in the problems and find the solution for them. Your analysis would be based on the gathered data.
4. Determine the Costs
There are some security problems that may cost a lot of money. Especially if you are going to be replacing some things that may have been damaged. It is also best to determine how much everything may cost. Anything that can still be manageable should at least be given a backup just in case. This would of course still cost you some.
5. Give out the Steps
This is the part wherein you are going to be writing down the steps to solving the severity of the issue. If the issue may be fixed in a cyber manner or in reality. List down the steps that you took to solve the issue.
FAQs
Why is a security risk assessment important?
It helps the people in charge to look for the problems that may cause the security to falter.
How do I know if my security is bad?
By doing a security risk assessment. You are testing out the severity of the risk you may be dealing with.
Is there a way for me to know if the assessment was a success?
The results may vary depending on how you did the assessment. But if you have followed all the steps you took making your assessment, there is a higher chance your assessment came out a success.
Security breaches can be scary. Especially when you have no idea how to solve them or if you have no idea how it may have happened. These things can come and go and often would leave you wondering how to solve it. Of course, some would get cautious when having to go through the same thing again. To be able to know that you are having the same issue, you must do a security risk assessment. Check the details, gather them, understand them. Find a solution and be always cautious.