9+ Security Incident Report Examples to Download
A security incident report is a critical document used by organizations to record the details of unusual events that pose a threat to the security or integrity of the institution or its assets. This report helps in understanding what happened, determining the impact of the incident, and developing strategies to prevent future occurrences. Whether it’s a breach of data, unauthorized access, or theft, effectively documenting every aspect of the incident is vital for internal investigations and compliance with legal requirements. By maintaining a clear and thorough record, organizations can ensure a swift response and strengthen their overall security measures
What is Security Incident Report ?

Security Incident Report Format
Incident Details
Date and Time of Incident
Location of Incident
Reporter’s Name and Contact Information
Incident Description
Detailed Description of What Occurred
Type of Incident (e.g., breach, theft, vandalism)
Parties Involved
Immediate Actions Taken
Initial Response
Containment Actions
Impact Assessment
Impact on Operations
Data or Assets Affected
Follow-up Actions
Security Incident ReportInvestigative Measures
Preventative Steps to be Implemented
Documentation
Attachments (photos, videos, documents)
Signature of Reporting Officer and Date
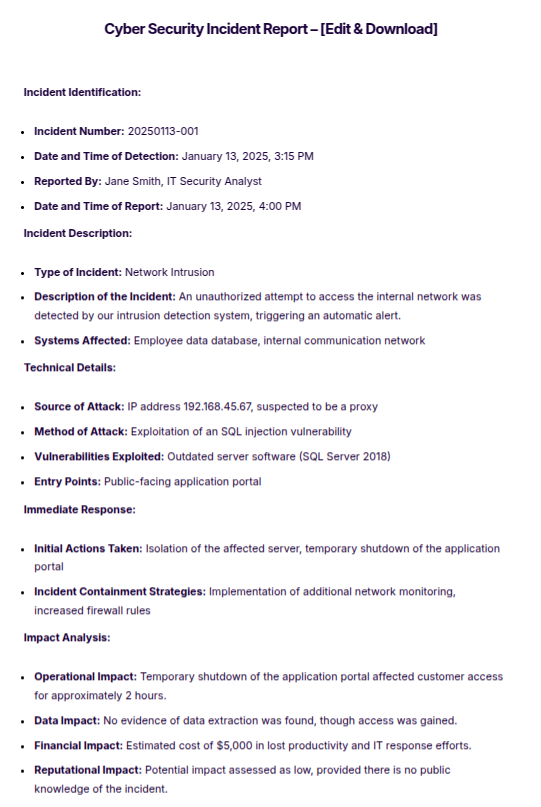
Security Incident Report Example
Date and Time of Incident: January 13, 2025, 2:30 PM
Location of Incident: Main Server Room, Building 9
Reporter’s Name and Contact Information: John Doe, Security Manager, Phone: 555-1234
Detailed Description of What Occurred: Unauthorized access detected in the main server room. Security alarms triggered at approximately 2:25 PM, with CCTV footage showing an unidentified individual tampering with server equipment.
Type of Incident: Unauthorized Access
Parties Involved: Unidentified individual, captured on CCTV
Initial Response: Security personnel responded to the alarm within five minutes, securing the area and initiating a lockdown of the server room.
Containment Actions: All systems were checked for tampering; critical data was backed up immediately to prevent potential data loss.
Impact on Operations: Temporary disruption to network traffic; no data loss confirmed.
Data or Assets Affected: Main server equipment and network integrity.
Investigative Measures: Review of CCTV footage and security logs ongoing; local authorities notified and a forensic analysis scheduled.
Preventative Steps to be Implemented: Upgrade of security protocols, additional surveillance cameras to be installed, and enhanced access controls for sensitive areas.
Attachments: CCTV footage file, security log excerpts from the incident day.
Signature of Reporting Officer and Date: John Doe, January 13, 2025
Security Incident Report Examples
Cyber Security Incident Report
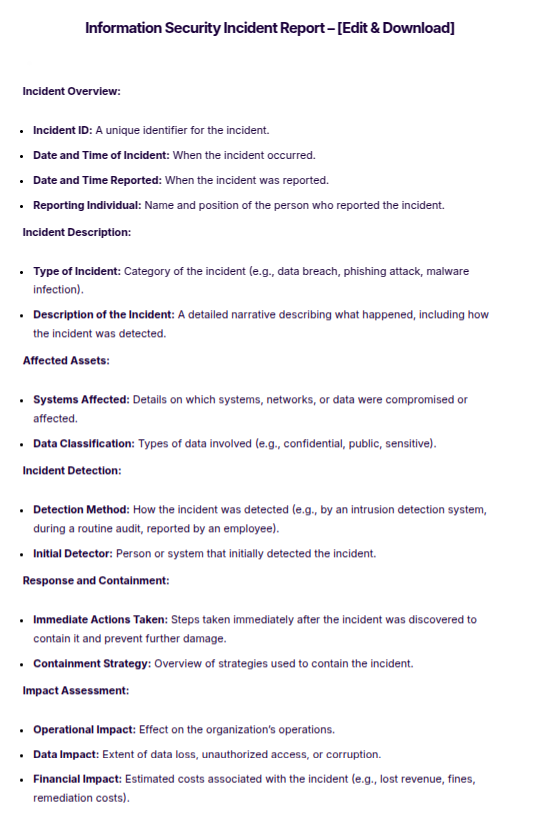
Information Security Incident Report
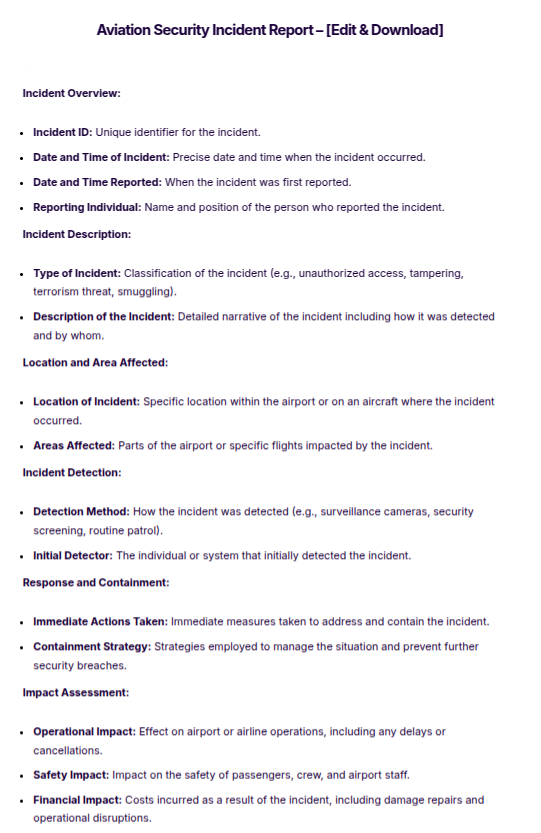
Aviation Security Incident Report
Security Incident Report Template
Construction Security Incident Report Template
Security Incident Response Plan Template
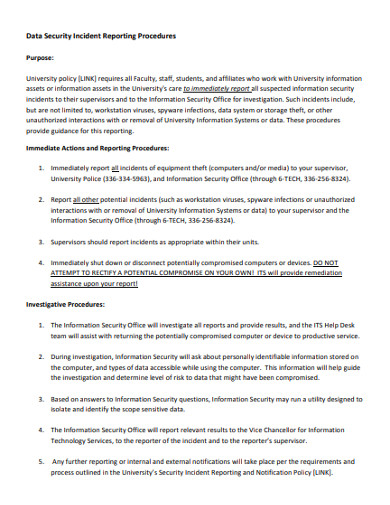
Data Security Incident Reporting Procedures
Data Security Incident Response Report
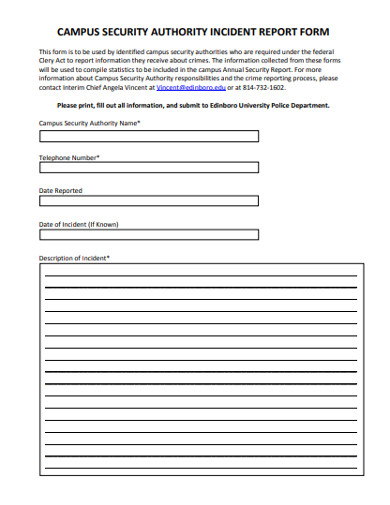
Campus Security Authority Incident Report Form
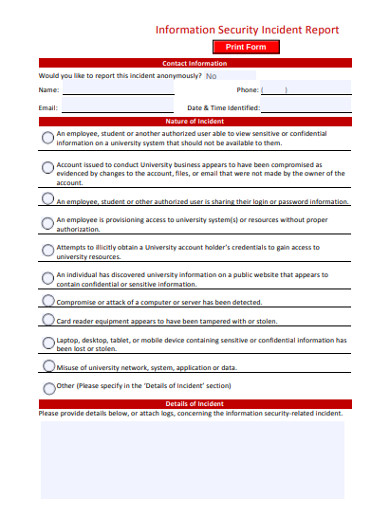
Information Security Incident Report
How to Write a Security Incident Report
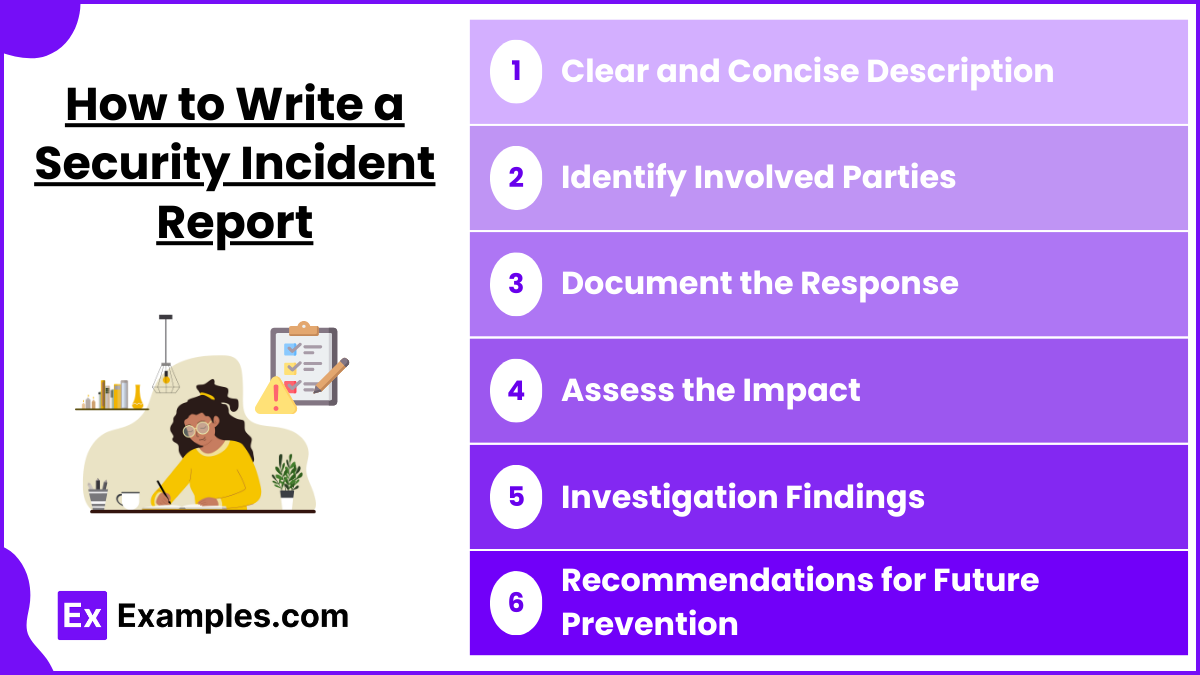
Writing a security incident report involves a systematic approach to accurately and comprehensively describe the events and aftermath of a security breach or incident.
Clear and Concise Description
Begin with a clear and concise description of what happened. Include the date, time, and location of the incident, along with a detailed account of the events. Avoid technical jargon and explain the incident in a way that is easily understandable.
Identify Involved Parties
List all individuals involved, including witnesses, victims, and suspects, if applicable. Provide their names, contact information, and their role in the incident.
Document the Response
Detail the immediate actions taken following the incident, such as notifying law enforcement, isolating affected systems, or administering first aid. Describe any steps taken to secure the area or mitigate further damage.
Assess the Impact
Evaluate and document the impact of the incident on operations, data security, and personnel. Discuss any disruptions to business processes and estimate financial losses if applicable.
Investigation Findings
Summarize the findings of any investigation conducted, including how the incident occurred and the vulnerabilities exploited. Provide information on evidence collected, analysis performed, and conclusions drawn.
Recommendations for Future Prevention
Propose measures that could prevent similar incidents in the future. These might include changes in policy, additional training for staff, upgrades to physical or digital security measures, or recommendations for monitoring and compliance.
Tips for Writing Security Incident Report
- Be Timely: Write the report as soon as possible after the incident to ensure that details are accurate and not forgotten. Prompt reporting also helps in taking immediate remedial actions.
- Use Clear Language: Avoid using overly technical terms or jargon that might confuse readers who are not familiar with security terminology. Keep the language simple and direct to ensure that all potential readers understand the report.
- Be Objective and Factual: Stick to the facts and avoid making assumptions or judgments. Describe what happened based on evidence and observations, not personal opinions.
- Include Specific Details: Provide all relevant details such as the date, time, location, and description of the incident. Also include details about the parties involved, actions taken, and the outcome.
- Maintain Confidentiality: Be mindful of privacy and confidentiality issues. Do not include personal information of individuals involved unless it is crucial to the report and appropriate permissions have been obtained.
- Recommend Improvements: Based on the incident, suggest practical steps or improvements to prevent future occurrences. This could include changes in procedures, enhancements in security infrastructure, or staff training initiatives.
FAQs
Who should write a Security Incident Report?
The person who detected the incident or a designated security officer should write the report.
When should a Security Incident Report be filed?
The report should be filed immediately after the incident is contained and all immediate responses are completed.
What should be included in a Security Incident Report?
Include the date, time, description of the incident, actions taken, affected assets, and recommendations for future prevention.
Why is it important to file a Security Incident Report?
Filing a report helps in managing and mitigating security risks, fulfilling legal requirements, and preventing future incidents.
How long should a Security Incident Report be kept?
Keep the report as long as organizational policies or legal requirements dictate, typically several years.