Authorization Request Letter Examples to Download
We all have experienced a situation where we have to get a very important business document on someone’s behalf. And, getting what we are tasked to get is not that easy to do. Clerks, administrative staff, or front desk attendants will surely request a letter that states the permission or consent, from the owner to the representatives, before giving them clearance regarding the claims. So before dashing forward to completing such an errand, we have to have a requisition for your authority, which should be sent and responded by document owners or any person in authority.
4+ Authorization Request Letter Examples
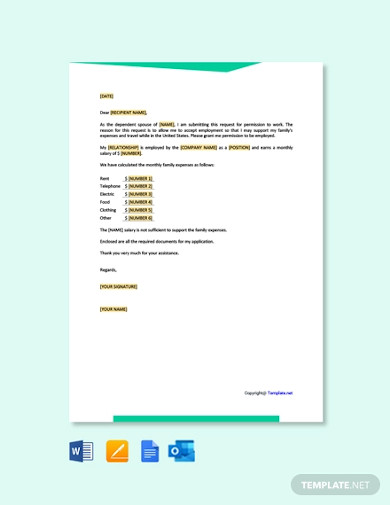
1. Free Request for Work Authorization Letter
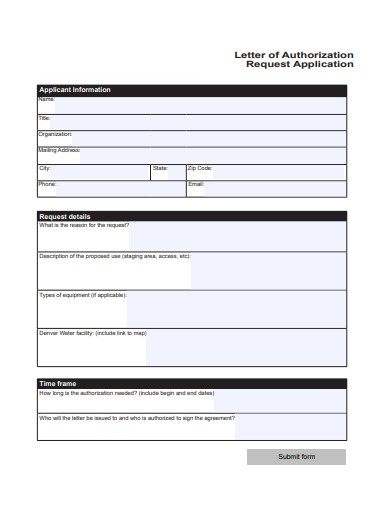
2. Letter of Authorization Request Application
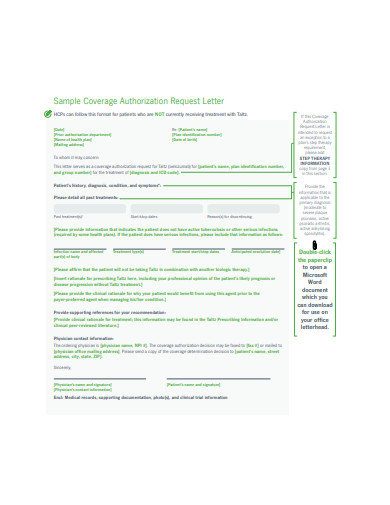
3. Sample Coverage Authorization Request Letter
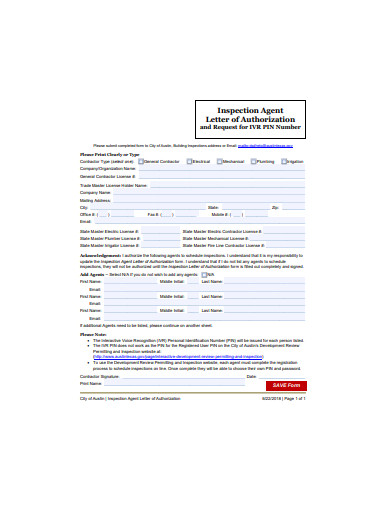
4. Authorization Request Letter Example
What Is an Authorization Request Letter?
An authorization request letter is a formal letter that is used to obtain the right to acquire or perform a specific item or task, respectively. The social networking site ManagementMania defined authorization as a security means used by all businesses to set perimeters to people’s accessibility to information, system, properties, and other company assets. With that being said, authorization request letters are must-have to get past authorization as described by the aforementioned site.
Authorization Management in GRC Platforms
Governance, risk management, and compliance (GRC) platforms help mitigate the risk that every organization may face. Not just that, they also help in the supervision of operations and legalities of corporate entities. Even though the platforms’ coverages are highly distinctive to each other, authorization management is undeniably common to all three. Martin Kuppinger said in his article entitled “Going beyond attestation: Authorization management is key,” that the ability of an organization to attest is crucial and highly beneficial. In the same article, authorization management helps map out profiles, ensuring more centralized governance. It is because of the same reason that any probability of risks’ occurrences is lowered.
How To Write a Formal Authorization Request Letter
A formal letter, like the authorization request letter, must follow a format. The method of formatting makes sure that your document meets the standard quality, which most professionals are very particular of. Typefaces, fonts, indentions, and spacings play very important roles in making your composition look formal. However, there are more factors that need to be put into consideration to achieve such an attribute. These factors include your tone, organization of thoughts, and grammar. Below, we have prepared our set of guidelines to give you a reference in writing a formal authorization request letter.
Step 1: Select a Format
As mentioned above, you have to follow a certain format when writing your authorization request letter. There are four formats to choose from, including the informal request letter format, modified block style, semi-block style, and full block style. The full block is the most preferred by writers who want their request letters to look very formal. Modified block style is for those who want their documents to appear a little less formal, whereas semi-block style is the perfect format for people who want their letter to look less formal than the ones which used full block style and a little more formal than the ones which used modified block style.
Step 2: Outline Request Points
Always create an outline of your request’s main points before actualizing it. Doing so helps you prepare all the pieces of information that you are going to need for your writing process. Furthermore, outlining your document’s details enables you to organize your thoughts on how to deliver your need for authorization right from the header, to the body, and the closing part of your letter.
Step 3: Compose Request With Emotion
Once you have already prepared all the specifics of your authorization request letter, then it is time for you to compose your document. Bear in mind that you have to determine what tone you will be using. Though this type of letter is meant to be formal, like memos and reports, you have to incorporate a touch of assertiveness and persuasiveness in delivering your request. This is so you can increase your chances of getting the rights you ought to have and of completing the task that comes with them.
Step 4: Include Enclosures
Most requests necessitate specific documents to be fastened. These could be photocopies of identification cards, received emails, receipts, warranties, and agreements. Attaching this paperwork proves that your purpose is legit.
Step 5: Proofread, Create a Copy, and Send
Just like any other paperwork, you have to proofread your output before finalizing it. Having done so aids you in determining and correct faults, such as grammatical and spelling errors, that you failed to notice during your composition process. Once edited, secure a soft and hard copy of your finished product, then send it to executives or people of authority.
FAQs
What do you mean by the authorization process?
The authorization process pertains to the act of granting permission to acquire or do something. In a business setting, it is used as a security proceeding that protects company properties.
What is the main difference between authentication and authorization?
Authentication is simply a process to verify a certain person’s identity, while authorization is the process that grants a particular person access to company resources. Authorization always comes right after authentication.
How is encryption related to authorization and authentication?
Just like authorization and authentication, encryption plays a vital role in every individual’s cybersecurity. The function of encryption is to transform readable data into an unreadable one. And, the only one who can transform the data back to its readable state is the individual who has a decryption key, usually data owners.
It has been clearly elaborated on how important authorization is, not just for business entities but also for every individual. This is why requesting to be granted with such a sensitive matter must be done in a careful manner. One minor mistake could deny the requester of the rights he or she needs to get important information, property, operational systems, and any other company resources. In addition, denial of such rights could also mean that the requester will fail to complete his or her tasks.